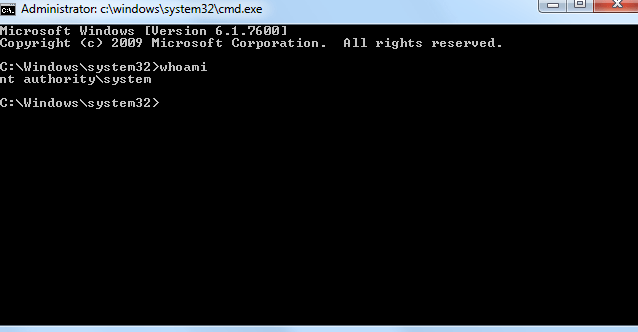
Remember my last post, the "SYSTEM" challenge? Now let's modify the scenario.... Imagine you've got the xp_cmdshell running under this account: os-shell> whoami do you want to retrieve the command standard output? [Y/n/a] y [21:52:27] [INFO] theQL query used returns 1 entries [21:52:27] [INFO] retrieved: dummydomain\\andrew command standard output [1]: [*] dummydomain\andrew Oh! This…
The road to “silver”