Windows service accounts are one of the preferred attack surface for privilege escalation. If you are able to compromise such an account, it is quite easy to get the highest privileges, mainly due to the powerful impersonation privileges that are granted by default to services by the operating system.
Even if Microsoft introduced WSH (Windows Service Hardening), there isn’t much you can do to “lower” the power of standard Windows services, but if you need to build or deploy a third-party service you can definitely strengthen it by using WSH.
In this post I will show you some useful tips.
Make use of Virtual accounts
Obviously a service must be run with a specific account. There are some built-in Windows accounts like SYSTEM (oh no !!), Local Service, and Network Service. But there is also the ability to use Virtual Accounts (I won’t write about “Group Managed Service Accounts” in this post) which are self-managed (no need to deal with passwords) and you can grant specific permissions by setting the correct ACL’s on the resources. This allows you to isolate the service and in case of compromise, they can only access the resources you have allowed. Virtual accounts can also access network resources, but in this case they will impersonate the computer account (COMPUTERNAME$)
Configuring Services with Virtual Accounts
First of all, you don’t need to create VSAs, when the service is installed, a matching account is automatically created for you in the form:
NT SERVICE\<service name>
all you need is to assign the account to your service:
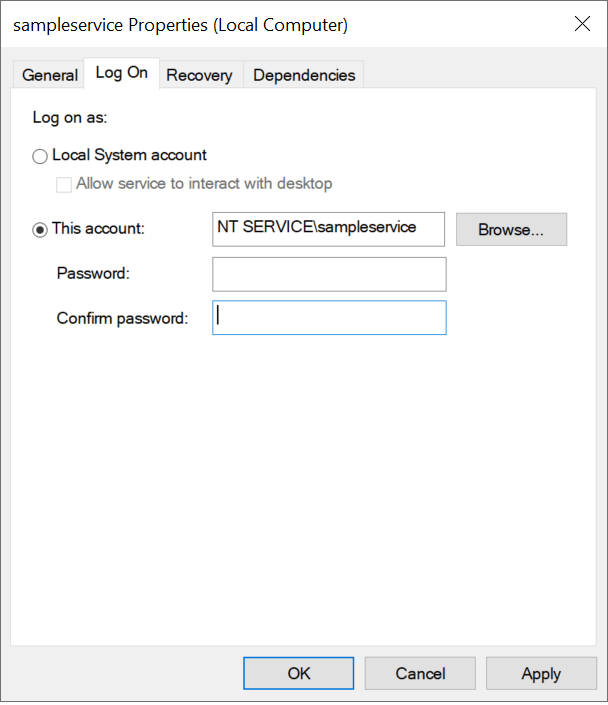
Don’t forget to leave the password field blank!
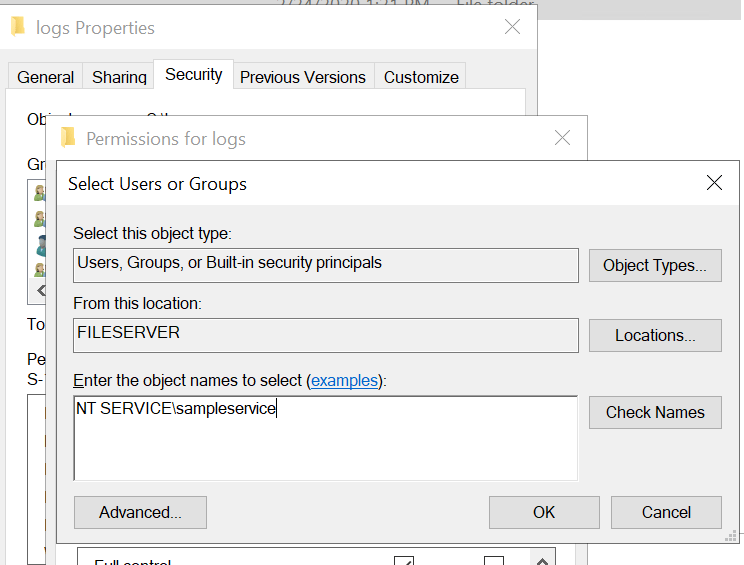
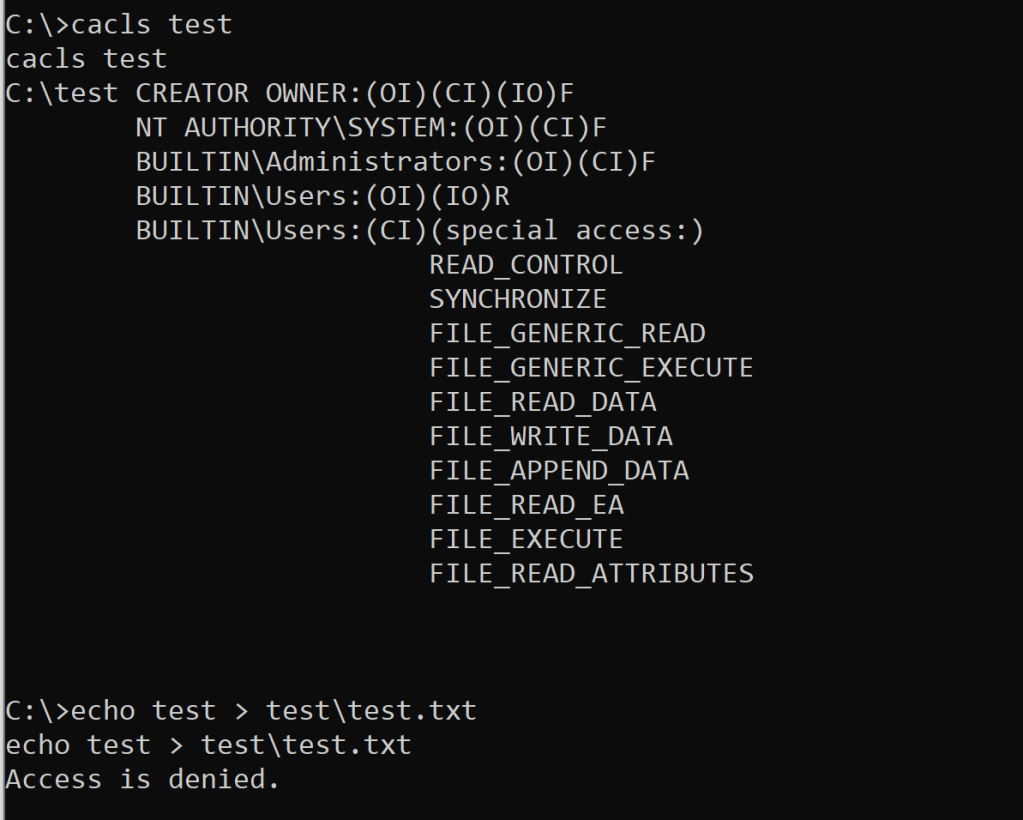
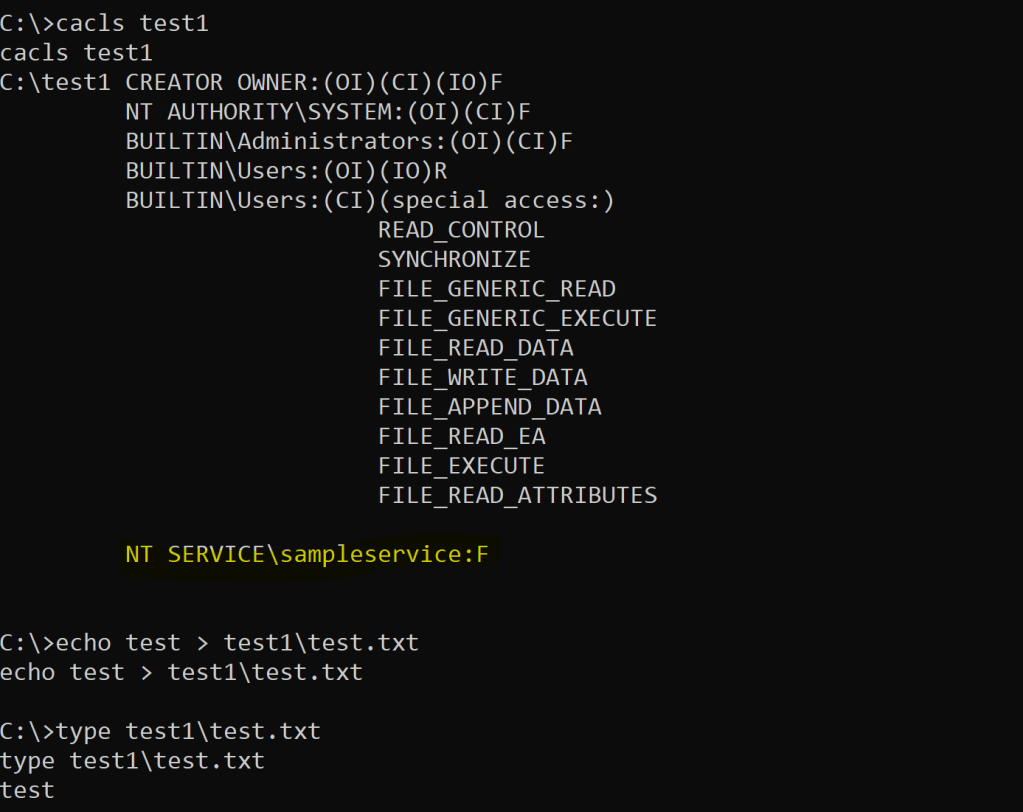
Restricting access to Virtual Accounts
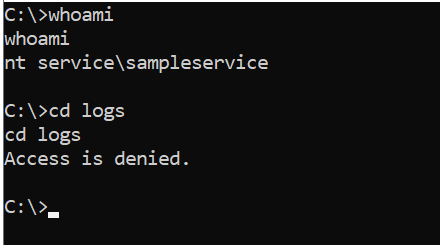
Now that your service runs under a specific account and not a generic one like Local Service or Network Service , you can implement fine-grained access control on resources like files and directories:

Removing unnecessary privileges
Impersonation privileges are a nightmare, so if your service doesn’t need to impersonate, why should we grant them to this service user?
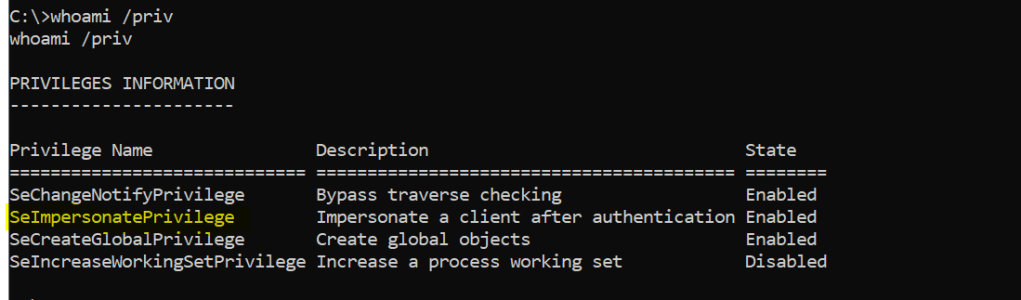
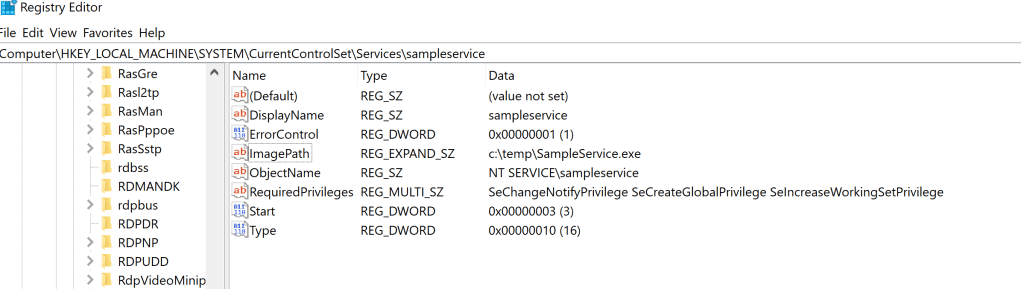
Is it possible to remove this default privilege? There is a good news, yes! We can configure the privileges directly in registry or by using the “sc.exe” command:
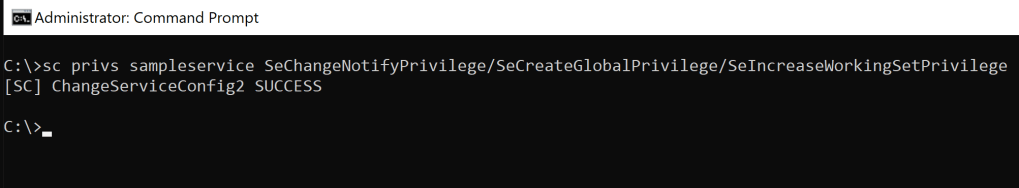
And these values will be written into registry:
Let’s see if the the privilege is removed:
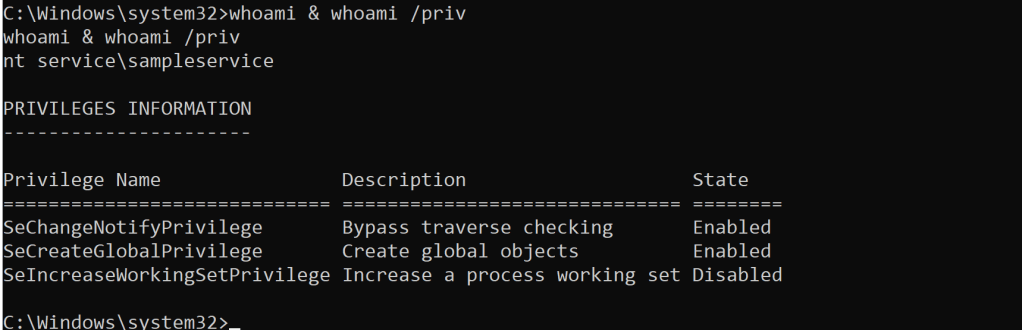
Oh yes! The dangerous privilege has been removed and it’s no more possible to get him back, for example using @itm4n ‘s trick described in this great post.
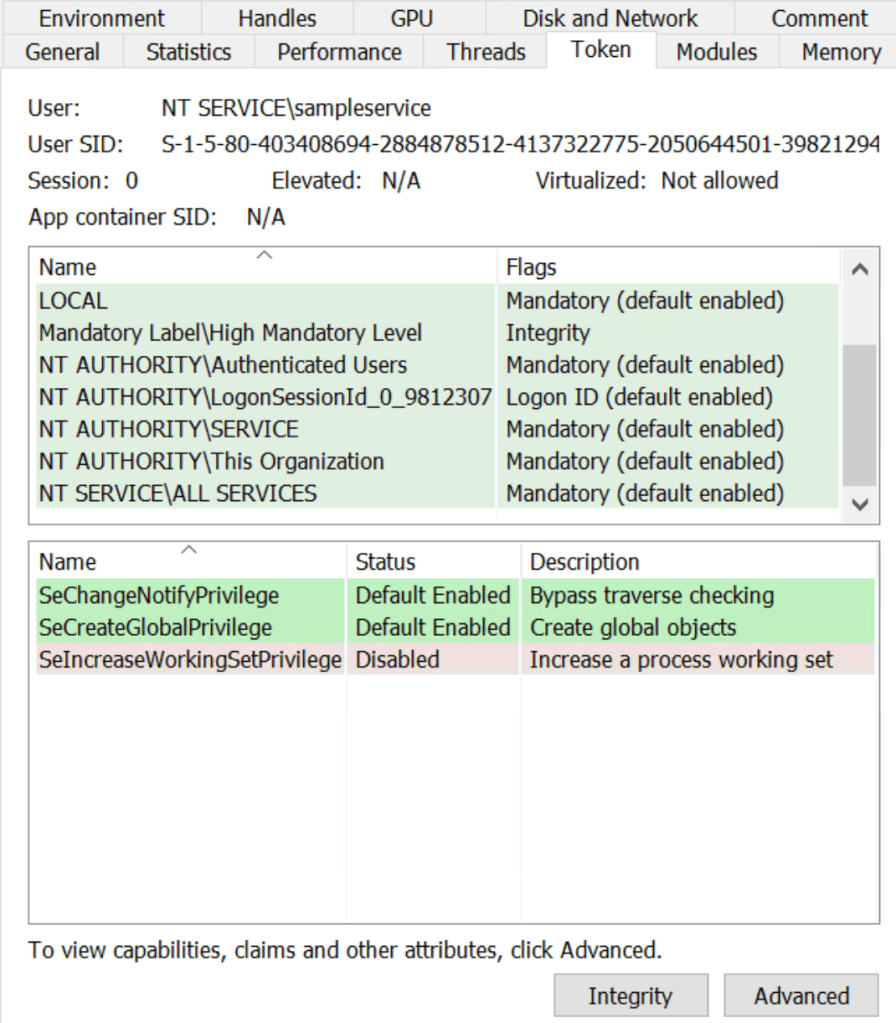
Write Restricted Token
If you add this extra group to your service tokens, you can further limit the permissions of your service account.
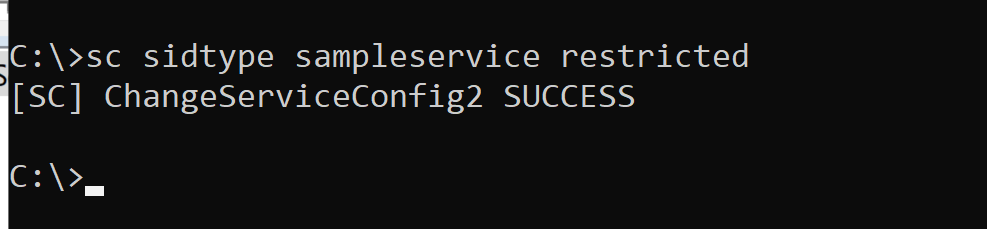
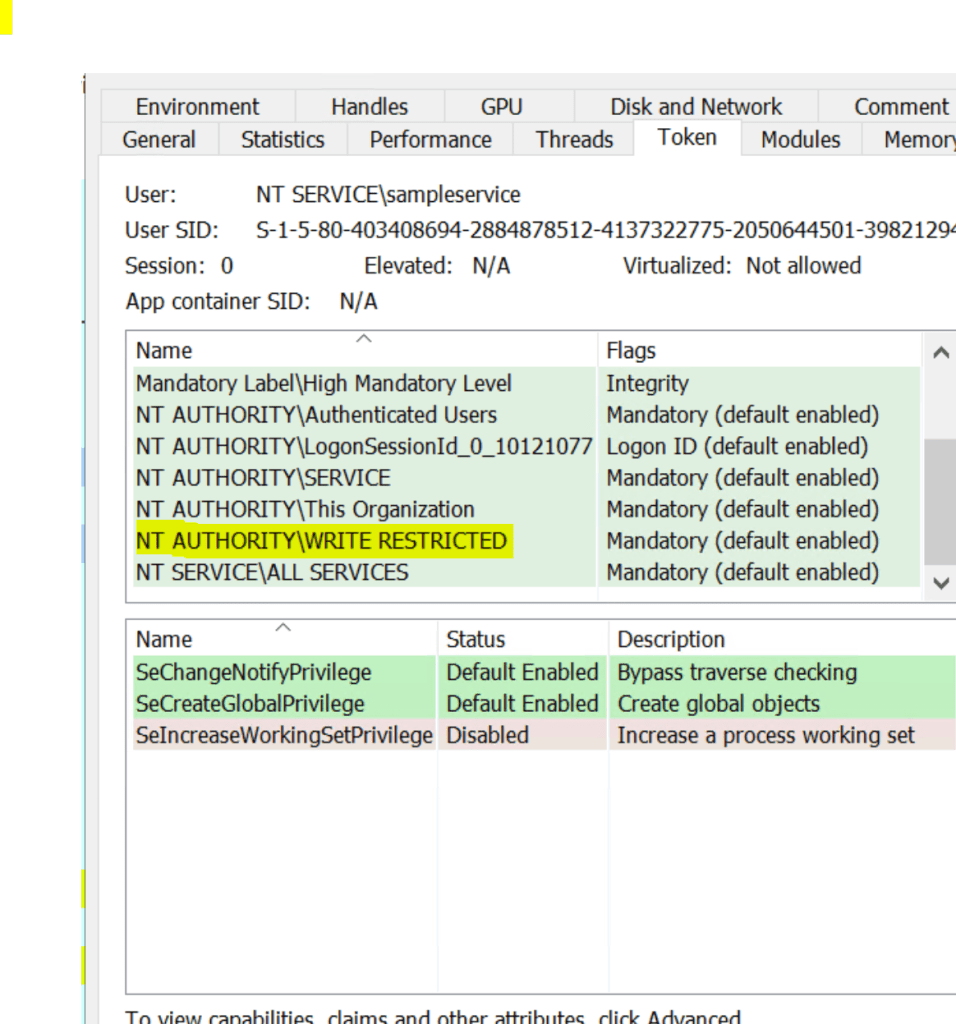
This means that by default you can only read or execute resources unless you explicitly grant write access:
A great research about write restricted tokens can be found in Forshaw’s post
Conclusions
I hope that this very short post can be useful for us who must secure our Windows Sytems (Offensive sec is just a joke for me 🙂 )
In the next post I will show you how to remove impersonation privileges in other critical services… stay tuned
UPDATE
Following Forshaw’s recent blog post and hint and his post on “Sharing a Logon Session a Little Too Much“ I can confirm that you gain back your privileges with the “loopback pipe trick”. This is possible because you will get the original token stored in LSASS without stripped privileges by the Service Control Manager. So the only solution to prevent this is to associate a Write restricted Token to your service?
Well not exactly … -> https://bugs.chromium.org/p/project-zero/issues/detail?id=2194
The use of WRITE RESTRICTED is considered by Microsoft to be of primary use for mitigating ambient privilege attacks 😦
That’s all 😉
“Offensive sec is just a joke for me” is indeed right ! I worked for 10+ years in offsec and for the past five years are more am focused into defending. Comparing offsec to blueteaming is like comparing derivative (math) to integrals 🙂
Defensive side of security done properly is much much more demanding.
LikeLike