Feedback Hub is a feature in Windows 10 which allows users to report problems or suggestions to Microsoft. It relies ond he “diagtrack” service, running as SYSTEM, or better known as “Connected User Experiences and Telemetry”
When the Feedback Hub gathers info in order to send them to MS, it does a lot of file operations, most of them performed by the SYSTEM user. It turns out that this application and the related services/executables which are run during the collection have a lot of logical bugs which can be exploited by “Directory Junctions” or Symbolic links via RPC Control.
These “bugs” could permit a malicious user to perform the following operations:
- Arbitrary File Read (Information Disclosure)
- Arbitrary File Overwite with contents not controlled by the Attacker (Tampering)
- Arbitrary File Overwite/Write with contents controlled by the Attacker (Elevation of Privilege)
- Arbitrary File/Folder Deletion (Elevation of Privilege)
In my investigations, I was able o perform all these operations in various circumstances.
Today I’m going to show you how it is possible to perform an Arbitrary File Overwite/Write which could easily lead to EoP. I found this issue in Windows 10 Preview up to Build v10.0.19592.1001. In Windows 10 “standard” version, the bug was much easier to exploit.
This issue was fixed in an “unintended” way in CVE-2020-0942 and sequent in latest WIP Build (10.0.19608.1006).
Prerequisites
- Standard Windows 10 / domain user with Windows 10 computer (virtual or physical)
- Diagnostics & Feedback has to be set to “Full” mode
- If “Basic” was selected at the first logon this can be changed by the logged on user in settings->privacy->diagnostics& feedback by switching from “required” to “optional”
Description
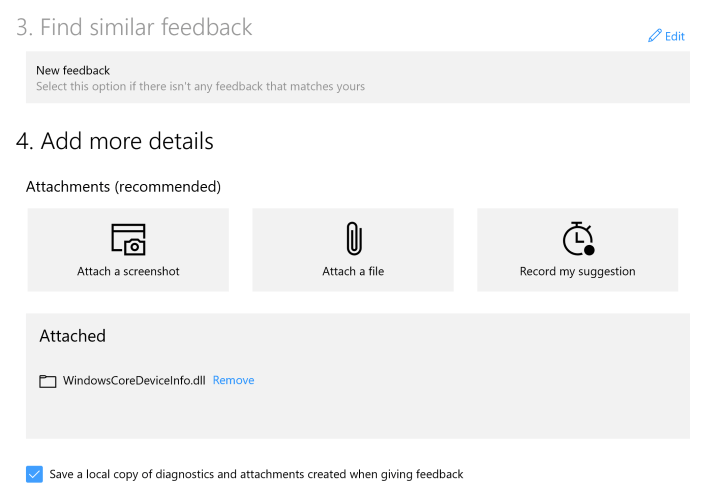
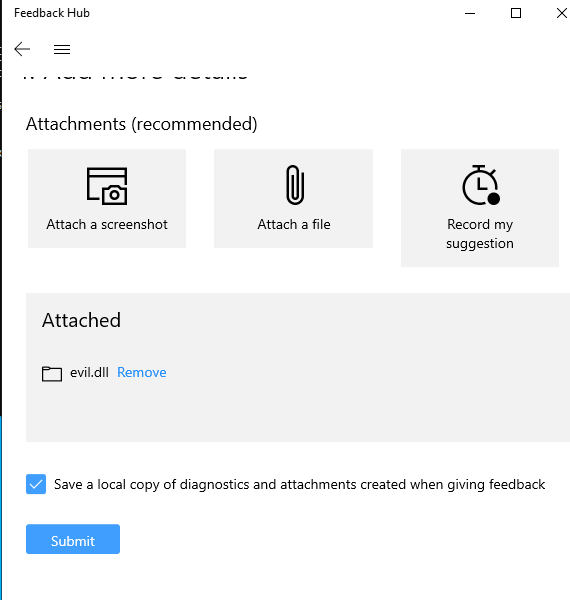
When an attachment is sent via the Feedback Hub App and you choose to “Save a local copy…”, several file operations are performed by the diagtrack service, mostly using SYSTEM user privileges.

Here is an overview of the most significant operations.
First, diagtrack service by impersonating the current user creates a temporary random folder name diagtracktempdir<XX..X> under the “c:\Users\user\Appdata\local\temp” directory:
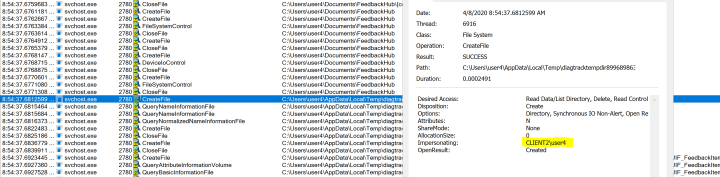
During the creation of the directory, the impersonated user also sets new permissions. These are not inherited from the parent folder and are very restrictive. In fact, as we can see in the following screenshot, permissions in the current directory do not include the current user:
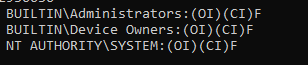
While, for the subdirectories and files inside, the current user has some privileges.

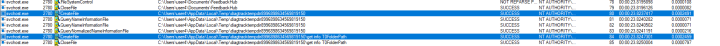
In the next screenshot we can observe that files and folders are created without user impersonation and therefore as SYSTEM. It should also be noticed that even the file uploaded as feedback attachment (windowscoredeviceinfo.dll in this case) is now copied in the temporary folder. Additionally, all the files and folders created or copied in the temporary path will inherit these new permissions.
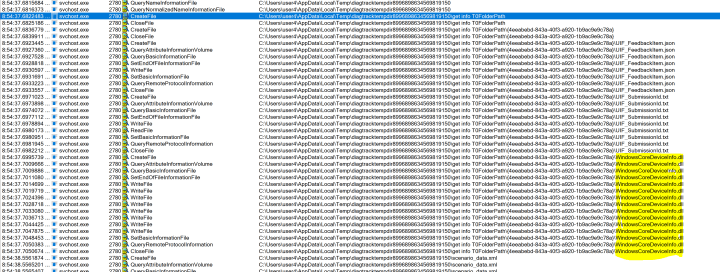
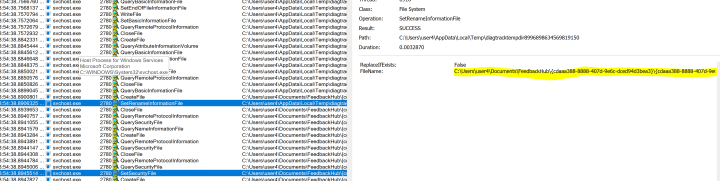
Once the process is complete, diagtracktempdir<XX..X> is renamed and moved into the current user FeedbackHub path. Sequent, restrictive permissions are again set on first directory of the renamed folder:
So the question is:
Is it still possible to abuse from special crafted “junction”?
Theoretically yes: the primary folder diagtracktempdir<XX..X> is created by the current user. Even though the permissions are sequent changed in a more restrictive way, such as granting the user only READ permissions, he could still modify because the user is the owner of the directory.
Practically, there is a race condition to win. Specifically, permissions on diagtracktempdir<XX..X> have to be changed before the subdirectories are created by SYSTEM without impersonation. In this way, the new permissions will be propagated, and the attacker will have full access on all of content.
Winning such a race conditions is hard. The time between the two events is in the order of milliseconds and you have to inject your “malicious” code for altering the permissions…
Nevertheless, I found a couple solutions to win the race conditions and developing a POC/tool in VS2019 C++
Note: In order to speed up the tests, always choose “Suggest a feature” in Feedback Hub.
Only 1 Hard disk present
I tested this procedure on both physical and virtual machines. Depending on the HW, performance and current workload, I was able to perform the exploitation at first run. In some cases, it took up to 10/15 attempts.
First of all, run the “Feedback Hub” app and exit. This will create the initial directory and settings if never launched before.
This is the “Logical Flow” of my Poc/Tool:
- Thread 1: Run a file watcher for the directory: “c:\users\<user>\AppData\Local\Packages\Microsoft.WindowsFeedbackHub_8wekyb3d8bbwe\LocalState\DiagOutputDir”
this will intercept the creation of a directory and save the directory {GUID} useful for later - Thread 2: Run a file watcher for the directory “c:\users\<user>\appdata\local\temp”
this will intercept the creation of folder diagtracktempdir<XX..X>- When the directory is created, change immediately the permissions, e.g.: everyone:full.
Note: SetSecurityInfo API function is not suitable because slow (it does a lot of useless work “under the hood”), NtSetSecurityObject is faster because more “atomic” - We know how the final path name will look like:
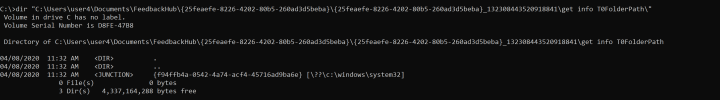
“diagtracktempdir<XX..X>\get info T0FolderPath\<{GUID}>”
- When the directory is created, change immediately the permissions, e.g.: everyone:full.
- Loop to create a “junction point” from the identified path to our target directory. Loop until the error is “path/file not found”.
If everything works fine, we should have copied our file in the destination directory. Alternatively, the loop will exit with an access denied error which means that we were too late.
The following screenshots are the PoC of how I was able to write the previous attached WindowsCoreDeviceInfo.dll in c:\windows\system32:
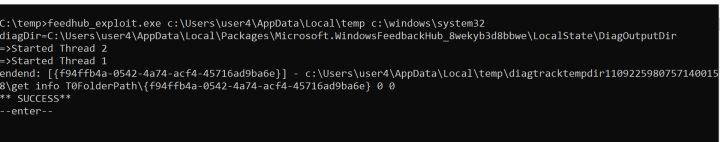
The following screenshot shows that the SetSecurity executed by the exploit happened before the creation of the directory “get info T0FolderPath
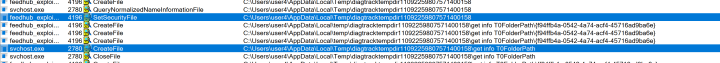
And directory successfully mounted:
Finally, file copied in target directory and EoP is just one step away 😉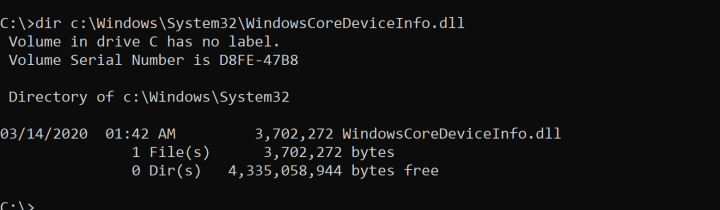
Two or more hard disk/partitions are present (including the possibility to mount an external USB disk)
I tested this procedure on both physical and virtual machines. In my test environment (physical and virtual machine with 2 partitions) I was able to perform the exploitation at first run. This solution is much more reliable.
Mounting an external USB disk on a physical machine can be accomplished by a standard user
First of all, run the “Feedback Hub” app and exit. This will create the initial directory and settings if never launched before.
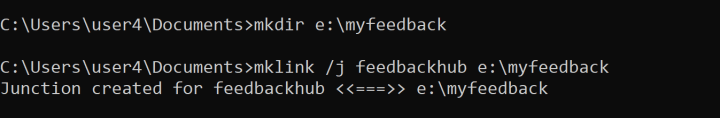
In this scenario, we will create a junction from the directory “c:\user\<user>\documents\feedbackhub” to a directory located on another drive. This will force “reparse” operations whenever a file is opened, and this introduces delays, especially if the junction points to a different drive/partition.
When a junction is in place, the user’s “…appdata\local\temp” directory is no more used and the diagtracktempdir<XX..X> directory is directly written under the feedbackhub.
The only prerequisite is that the feedbackhub folder has to be empty, which means that that no previous Feedback Hub with Local Saving Attachments have to be done, because once the folders and files are created, the user cannot delete them.
The following steps are required to win the race condition:
- Create the junction:
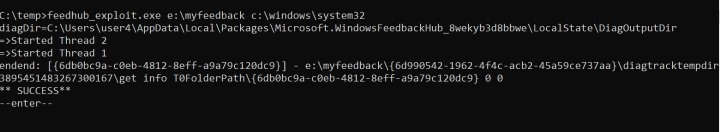
- Use the junction directory instead of “…appdata\local\temp” in the C++ exploit:
- Submit a new feedback and load a malicious DLL as attachment
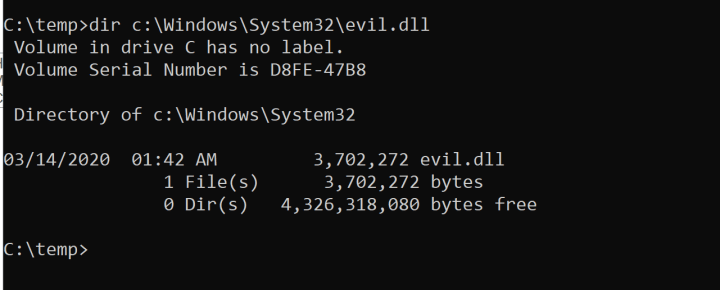
Et voilà! Our dll was copied in System32 folder:
Conclusions
This is just one of the still many possibilities to perform privileged file operations by abusing the generic “error reporting” functionalities in Windows 10.
If you’re hunting for for CVE’s maybe this might be worth a try. All you need is Procmon, time and patience 😉
POC can be downloaded here