In the last period, there have been several researches on how to escalate privileges by abusing generic impersonation privileges usually assigned to SERVICE accounts.
Needless to say, a SERVICE account is required in order to abuse the privileges.
The last one, in order of time, “Printer Spoofer” is probably the most dangerous/useful because it only relies on the “Spooler” service which is enabled by default on all Windows versions.
In Windows 10 and Windows Server where WinRM is not enabled, you can use our “Rogue WinRM listener” in order to capture a SYSTEM token.
And of course, in Windows Server versions 2016 and Windows 10 up to 1803, our Rotten/Juicy Potato is still kicking!
In this post I’m going to show you how it is possible to get SYSTEM privileges from the Network Service account, as described in Forshaw’s post “Sharing a Logon Session a Little Too Much“. I suggest you to read it before if not already done as I won’t detail the internal mechanism.
In short, if you can trick the “Network Service” account to write to a named pipe over the “network” and are able to impersonate the pipe, you can access the tokens stored in RPCSS service (which is running as Network Service and contains a pile of treasures) and “steal” a SYSTEM token. This is possible because of some “weird” cheks/ assignments in token’s Authentication ID. The token of the caller (coming from RPCSS service) will have assigned the Authentication ID of the service and if you impersonate this token you will have complete access to RPCSS process, including his tokens. (because the impersonated token belongs to group “NT Service\RpcSs “)
Side note: here you can find some other “strange” behaviors based on AuthID.
Given that the local loopback interface (127.0.0.1) is considered a network logon/access, it’s possible to exploit this (mis)behavior locally with an all-in-one tool.
The easiest way is a compromised “Network Service” account with a shell access and this will be our starting point. In this situation, we can directly write via the loopback interface to the named pipe, impersonate and access RPCSS process tokens.
Note: For testing purpose, you can impersonate the “Network Service” account using psexec from an admin shell:
- psexec64 -i -u “NT AUTHORITY\Network Service” cmd.exe
There are many ways to accomplish this task, for example with Forshaw’s NTOBJECTMANAGER library in Powershell (keep in mind that the latest MS Defender updates marks this library as malicious!??)
But my goal was to create a standalone executable in old plain vanilla style and given that I’m very lazy, I found most of the functions needed in the old but always good incognito2 project. The source code is very useful and educational, it’s worth the study.
I reused the most relevant parts of code and did some minor changes in order to adpapt it to my needings and also to evade AV’s.
Basically this is what it does:
- start a Named Pipe Server listening on a “random” pipe
- start a Pipe Client thread, connect to the random pipe via “localhost” and write some data
- In the pipe server, once the client connects, impersonate the client (coming from “RPCSS”)
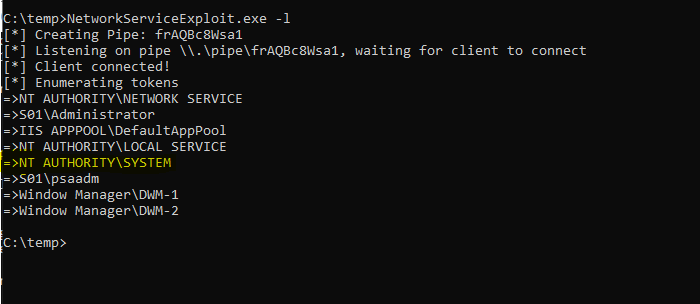
- List tokens of all processes:
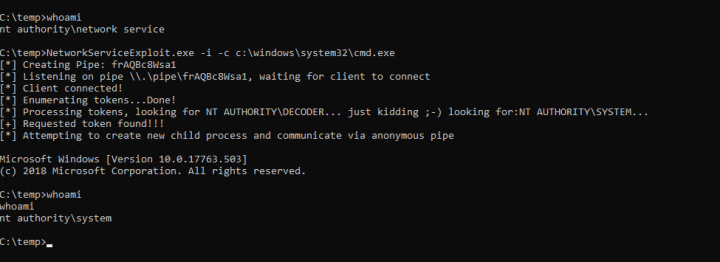
- If a SYSTEM token is available , impersonate it and execute your shell or whatever you prefer:
The “adapted” source code for my POC can be found here: https://github.com/decoder-it/NetworkServiceExploit
That’s all 😉