As promised in my previous post, I will (hopefully) give you some advices on how to harden the IIS “Application Pool” accounts aka “identities”.
First of all we need to understand how IIS architecture works and how identities are managed. Therefore I suggest you to read some specific posts about this topic for example this one and this one . More about identities can be found here
Ok! now that you got all the details let’s start from the IIS worker process “w3wp”. This is the process which will effectively access the http resources we asked for and serve them. By default this process runs under the “ApplicationPoolIdentity” identity. This is nothing more than (in this case the default) a “Virtual Account”, with the name of the Application Pool Identity, which IIS creates for us. Virtual accounts are directly managed by OS, so you don’t need to set passwords.
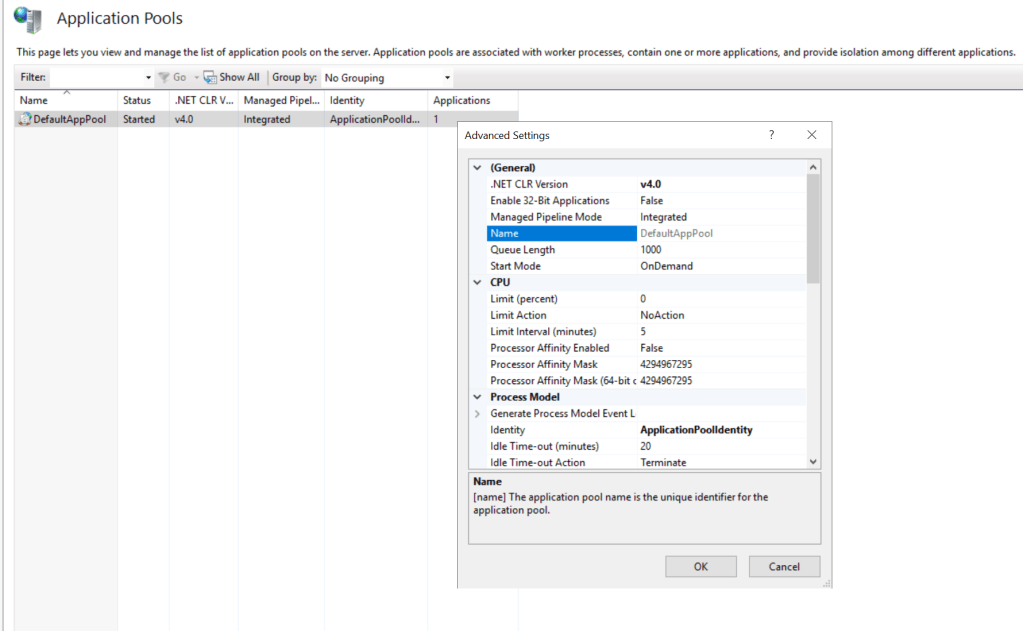
We can create dedicated Application Pools and assign them to web sites. Given that every application pool then has his own Virtual Account, we can secure access to resources based on the single application pool identity.

This is really cool, so we are able to set our security boundaries.
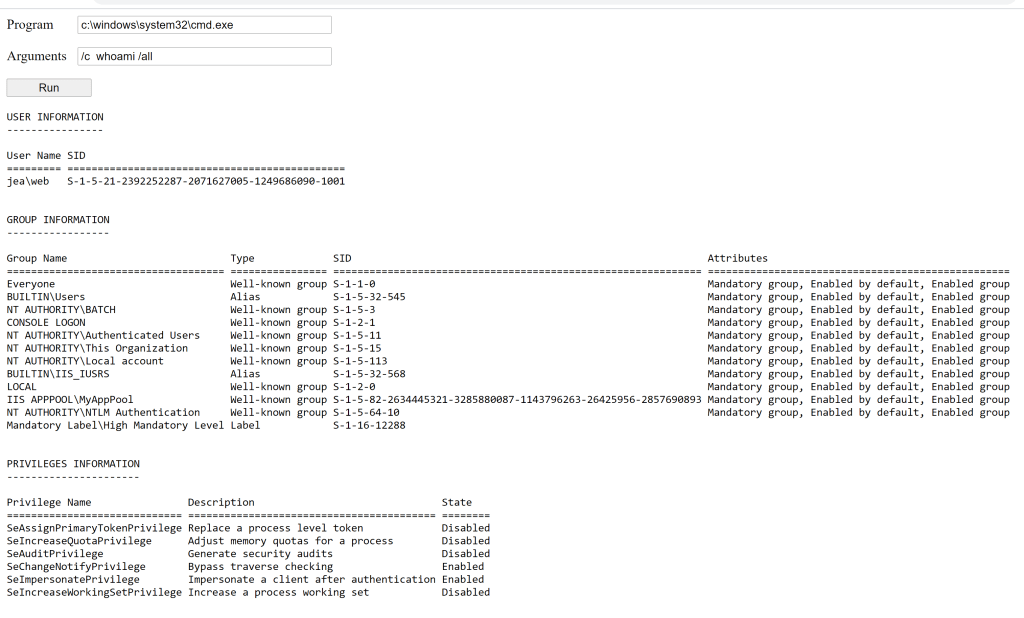
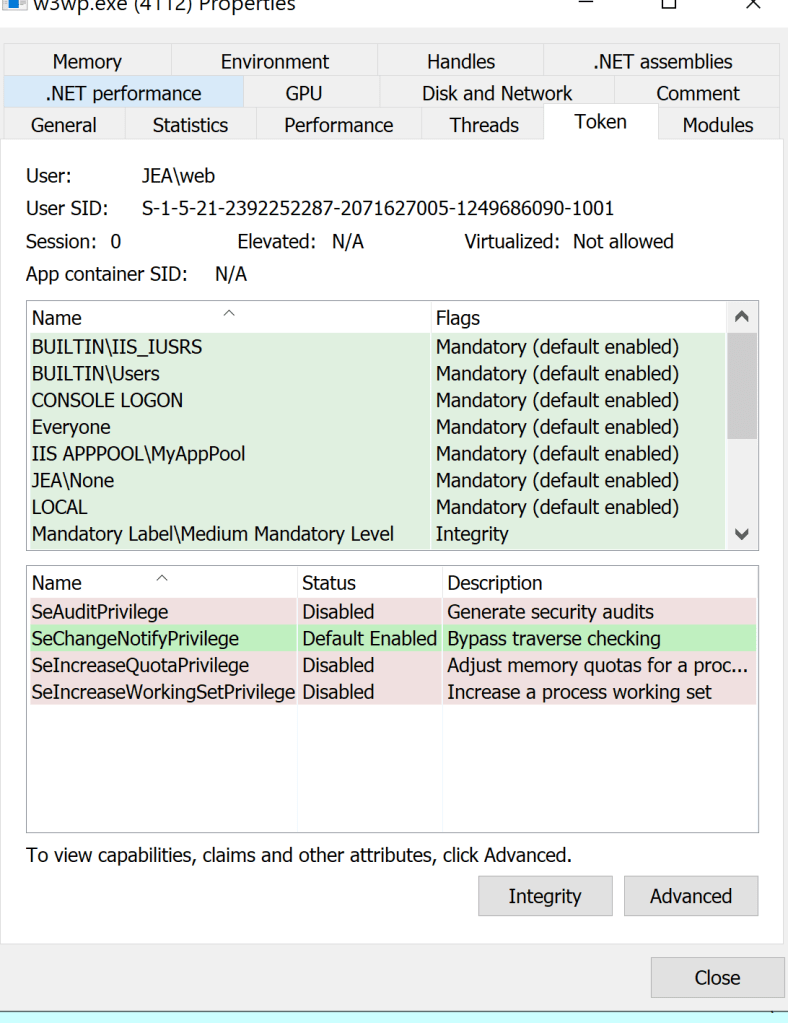
Let’s take a closer look at the process:
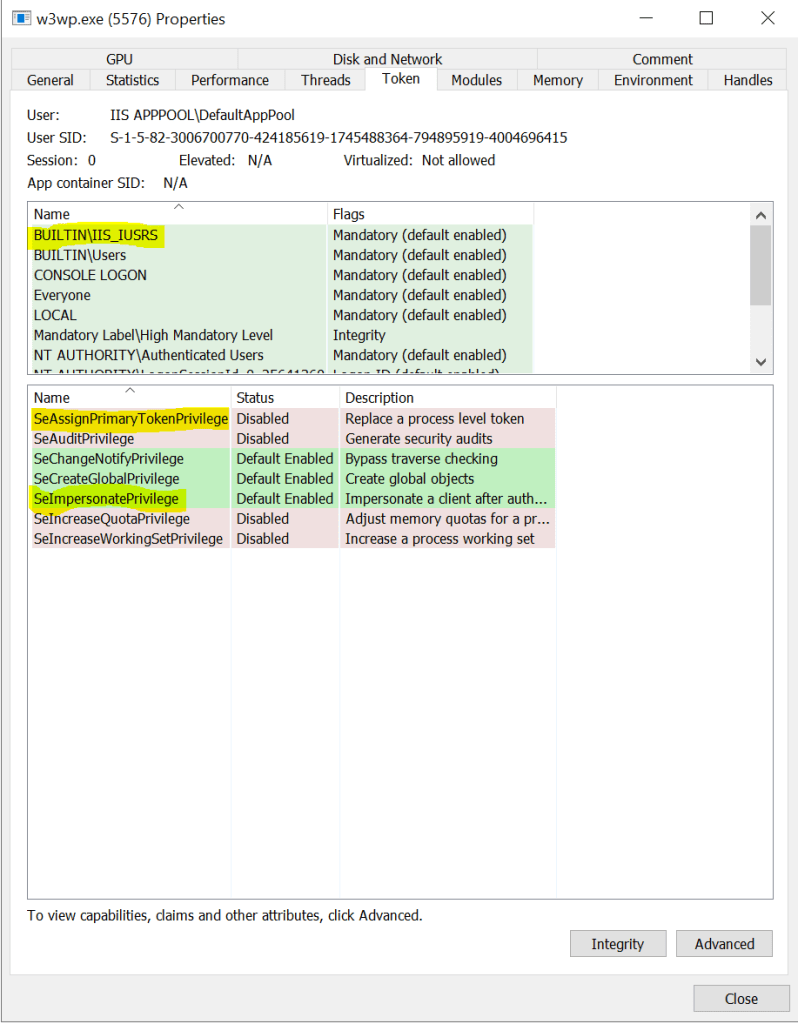
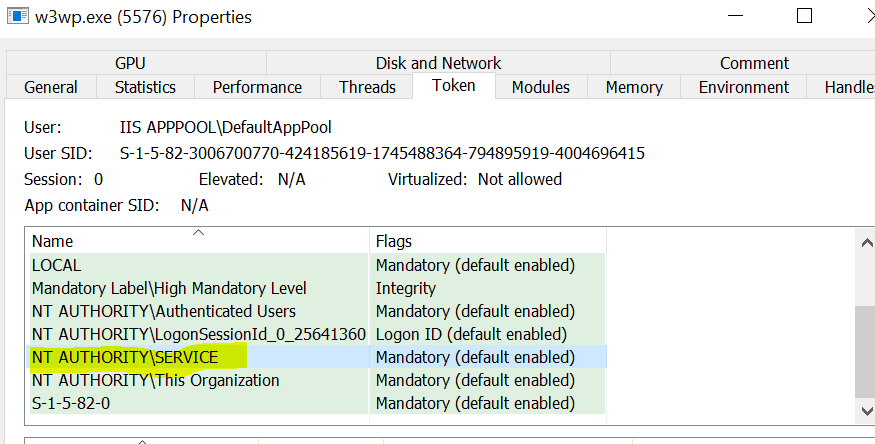
We can observe that the AppPool identity is member of the built in “IIS_IUSRS” group and also the “SERVICE” group. Unfortunately, it has also 2 dangerous privileges: SeAssignPrimaryTokenPrivilege and SeImpersonatePrivilege, probably the most abused privileges for escalations when you are able to get code execution on a buggy web application (in the following screenshot we uploaded a webshell), do you agree?
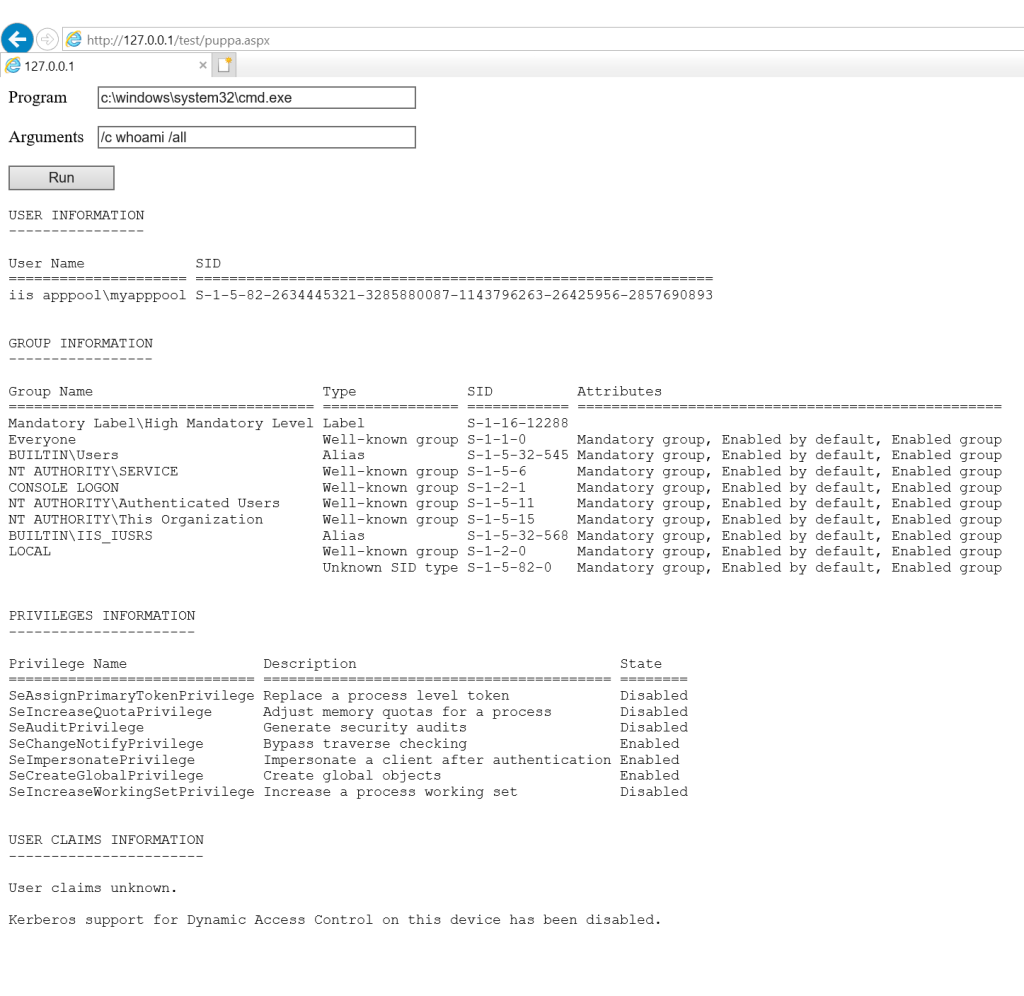
I think that everyone who is responsible / concerned for securing IIS Web Applications would like to limit these privileges, especially if they aren’t needed. In fact, the impersonation privileges are only useful if IIS needs to impersonate the Windows user who accessed the web app (<identity impersonate=true>), otherwise who cares?
So the first question is: is it safe to remove the privileges in this context?
There is no official documentation from MS about this, but there is not reason why it should lead to problems as long as you don’t need to impersonate
Now let’s see how privileges are configured.
We need to launch the Policy editor “gpedit.msc” and go to:
Computer Configuration->Windows Settings->Security Settings->Local Policies->User Right Assignment
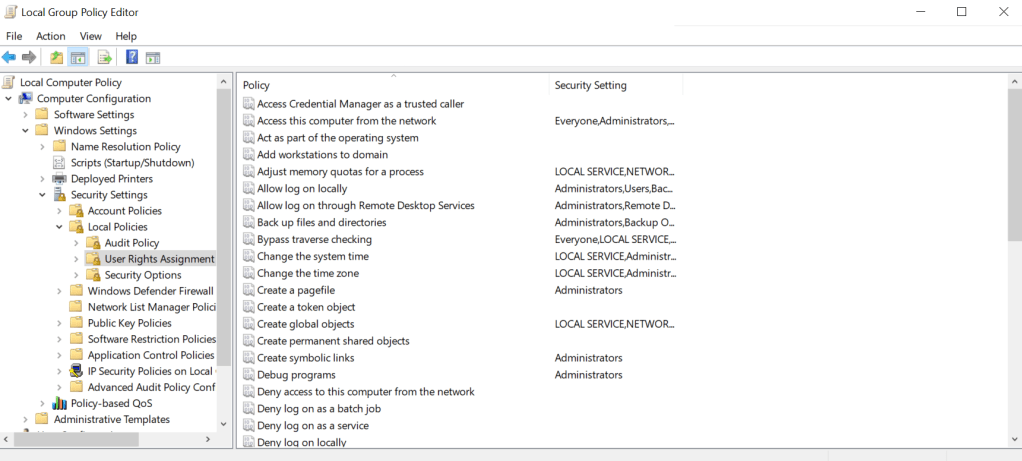
This is the configuration for the “Impersonate a client after Authentication” (SeImpersonatePrivilege):
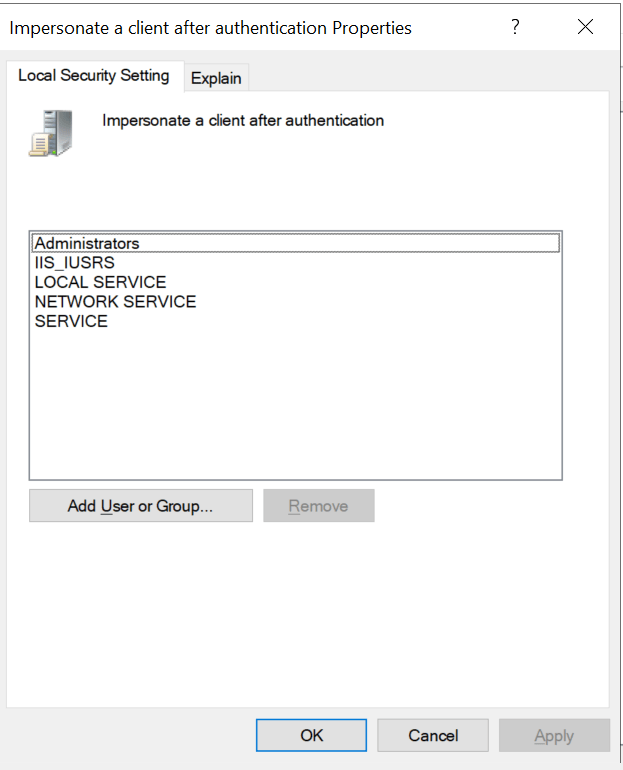
Bad news, IIS_IUSRS and SERVICE group have this privilege by default, and the Application Pools Identities belongs to these groups.
For the “Replace a process level token” (SeAssignPrimaryPrivilege) we have:
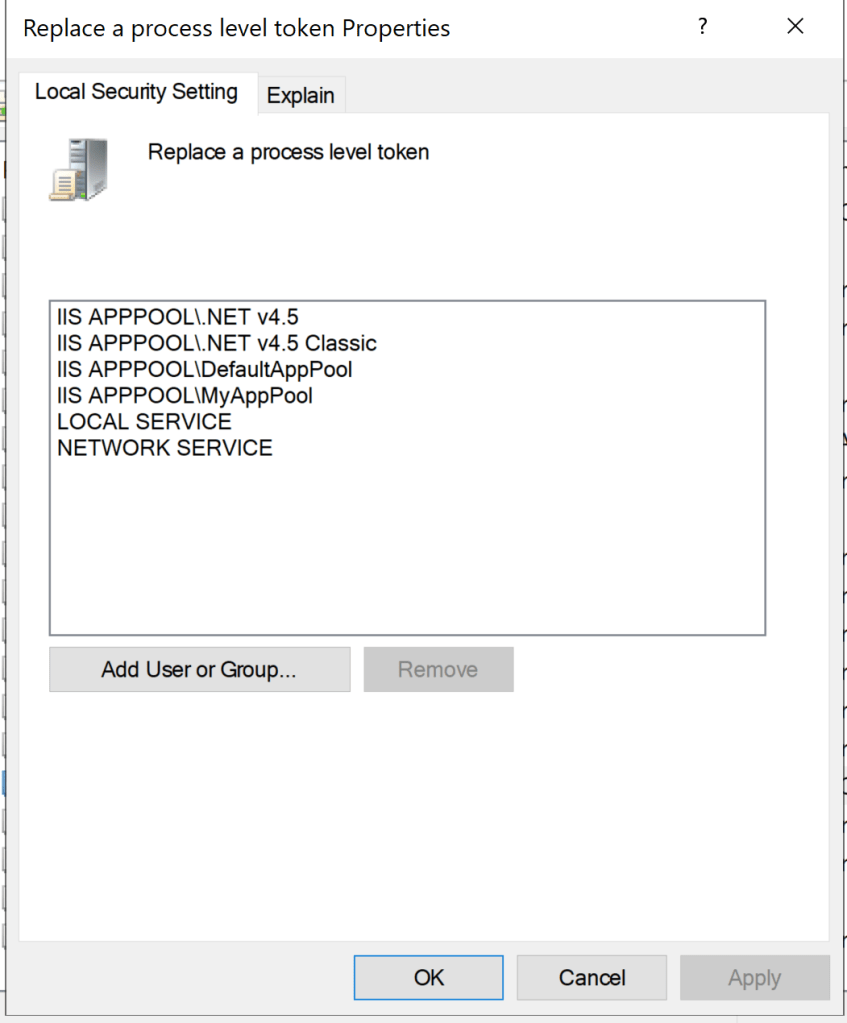
Again, our Applications Pool Identities and SERVICE groups have this privilege.
We could indeed inhibit the automatic membership to “IIS_IUSRS” group by modifying the appropriate xml file following MS official documentation (side note: I was not able to perform this action, got always an HTTP error 503 if set to “true”):
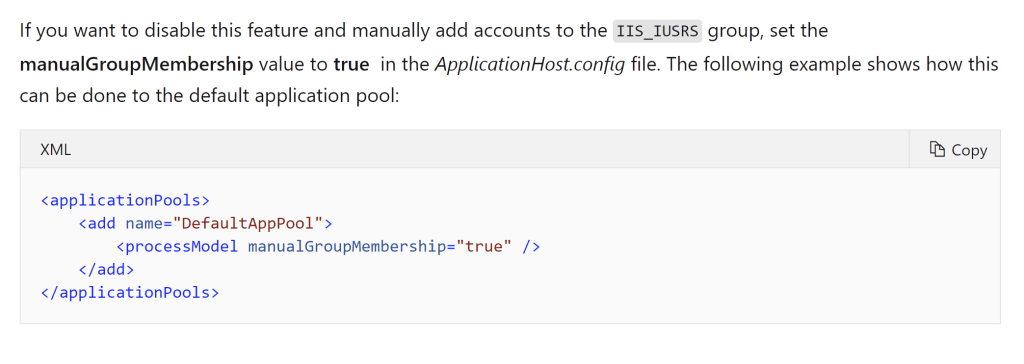
But this would not solve our problem given that the Application Pools Identities belongs to SERVICE group by default and we cannot remove this group from the Application Pool. Moreover, we cannot remove Impersonation Privileges for the SERVICE group.
So what can we do?
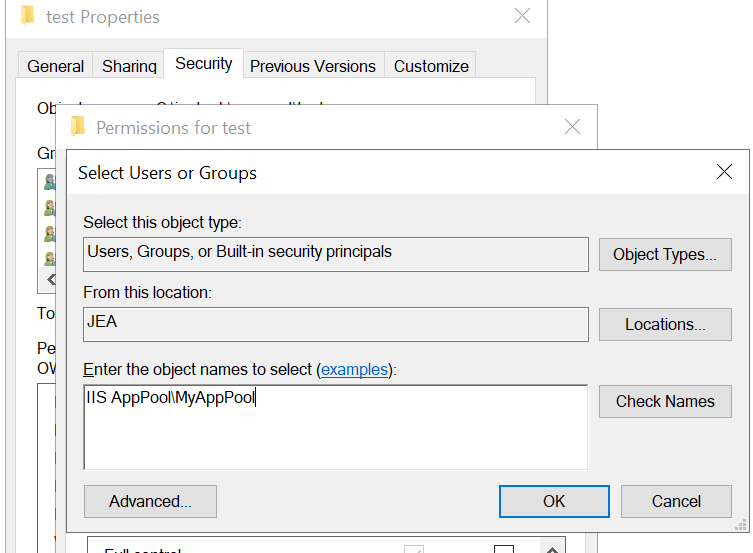
First of all we have to forget 😦 the Virtual Accounts and assign to our Application Pool a “real” Windows Account (just a standard user with a very strong password and set to “never expires”).

Let’s see the result:
The user (web) is no more member of the SERVICE group, this is a good starting point.
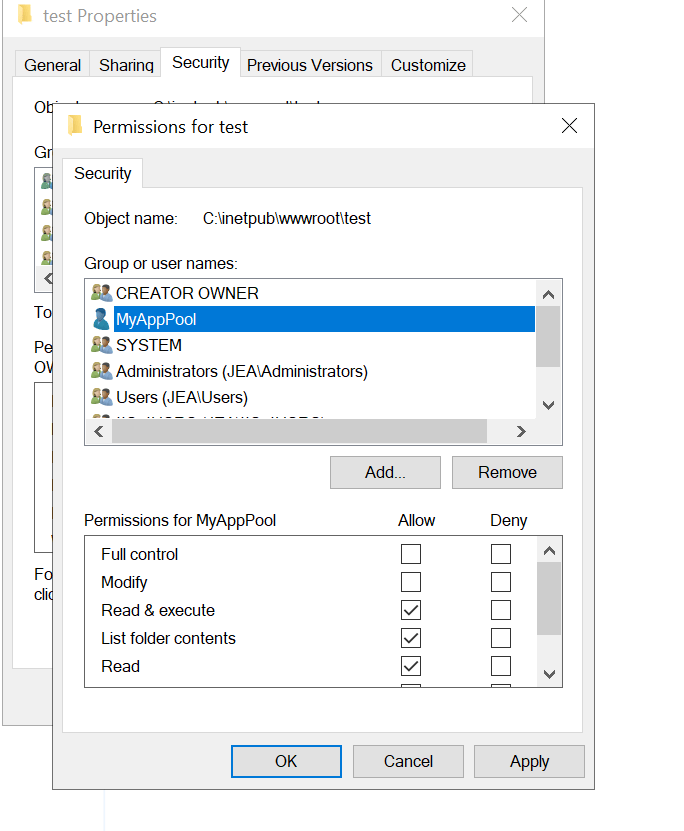
He is still member of IIS_IUSRS and IIS APPPOL\MyAppPool, so in order to remove our unwanted privileges, in the Group Policy Editor we have to:
- Remove IIS_IUSRS from “Impersonate a Client after Authentication”
- Remove IIS APPPOL\MyAppPool from “Replace a process level token”
- restart the IIS services and observe the result..
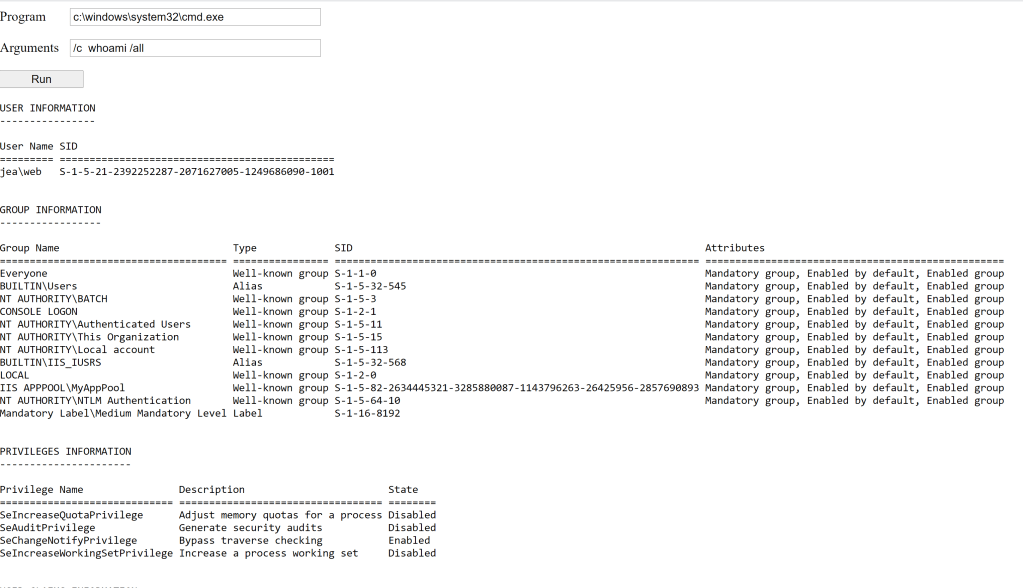
Yes! privileges are no longer present, and is confirmed by listing the w3wp process tokens:
Now we can be more comfortable given that we have secured these accounts, isn’t it? Well … not exactly.. there are still a lot af nasty things you can do in session 0 .. more about this maybe in a future post 😉
Hi, Thanks very much for the article. I would like to know how or which program are you using on those screenshots to get such details about the w3wp.exe properties. in Task manager when I click on properties, I don’t have all that information. Thanks
LikeLike
Process Hacker
LikeLike
Thanks very much.
LikeLike